Hack Like a Pro: How to Hack the Shellshock Vulnerability « Null
Por um escritor misterioso
Descrição
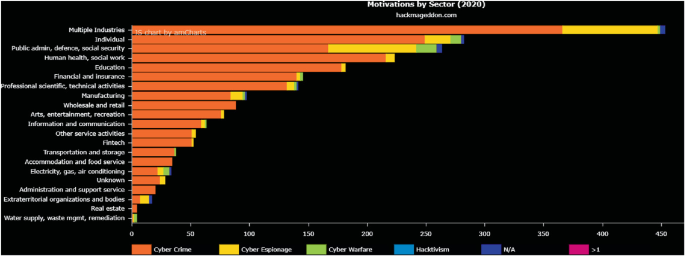
Determining Vulnerabilities of Pervasive IoT Devices and Their Geographic Distribution
3 Best Advanced hacking tools to find exploits automatically - Free + Linux
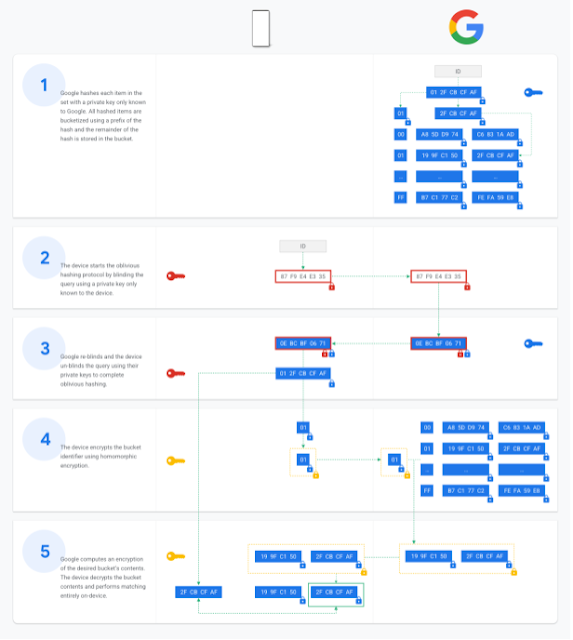
Google Online Security Blog: 2021

Kali Linux Web Penetration Testing Cookbook

TryHackMe Advent of Cyber 2 [2020]
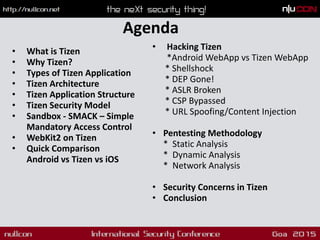
Hacking Tizen : The OS of Everything - Nullcon Goa 2015
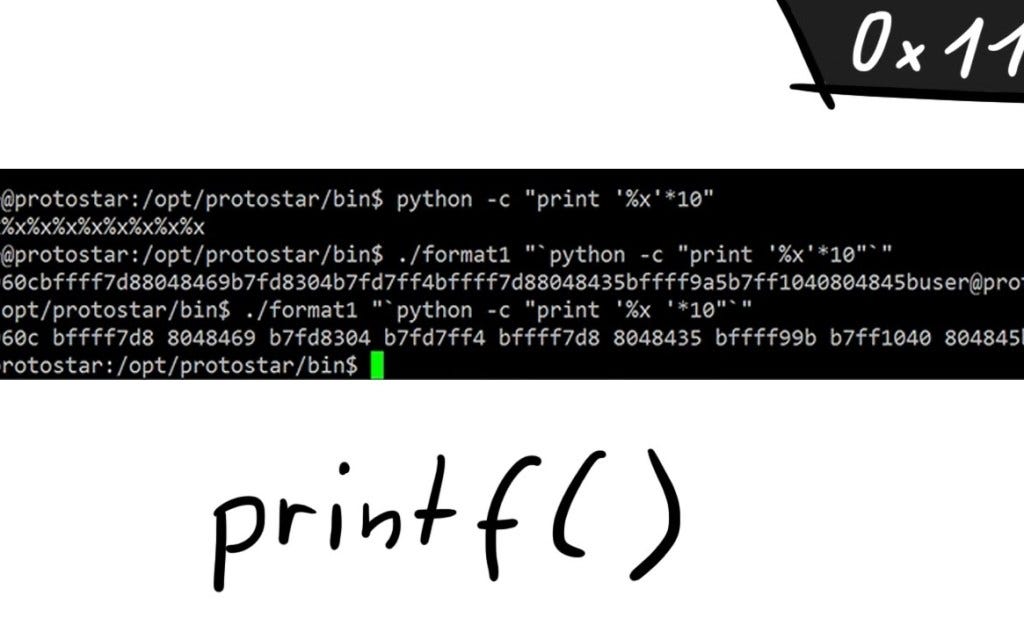
Format String Exploit. One of the most commonly used functions…, by ka1d0

BSidesJXN 2017 - Improving Vulnerability Management

Message Authentication and Provenance Verification for Industrial Control Systems
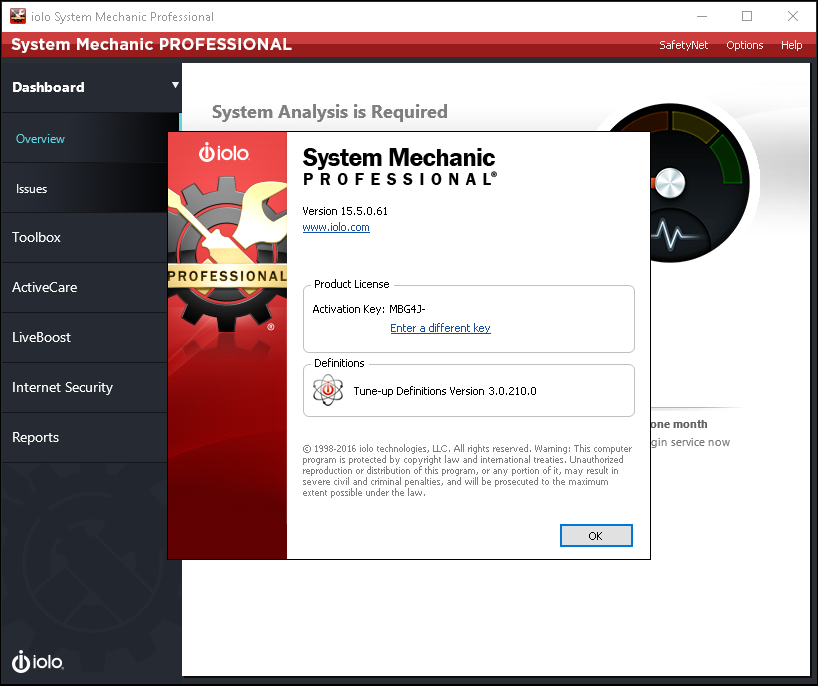
Exploiting System Mechanic Driver - VoidSec
de
por adulto (o preço varia de acordo com o tamanho do grupo)