A fuzzer and a symbolic executor walk into a cloud
Por um escritor misterioso
Descrição
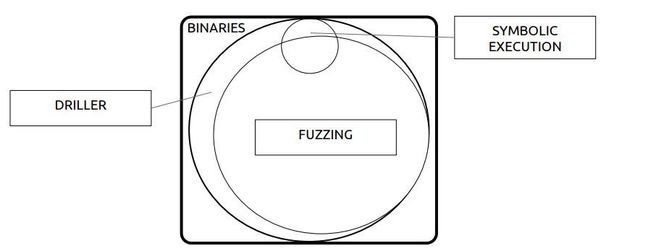
Finding bugs in programs is hard. Automating the process is even harder. We tackled the harder problem and produced two production-quality bug-finding systems: GRR, a high-throughput fuzzer, and PySymEmu (PSE), a binary symbolic executor with support for concrete inputs. From afar, fuzzing is a dumb, brute-force method that works surprisingly well, and symbolic execution is…

Fuzzing: Hack, Art, and Science, February 2020

Fuzzing: Hack, Art, and Science, February 2020

Recon2022 - Reverse engineering of black box binaries with symbolic and concolic execution technique
Hackers turn to angr for automated exploit discovery and patching • The Register

SAGE: Whitebox Fuzzing for Security Testing - ACM Queue

Fuzzing vulnerability discovery techniques: Survey, challenges and future directions - ScienceDirect

Capturing memory corruptions with symbolic execution - Introduction to KLEE (part 3)
GitHub - mishmashclone/wcventure-FuzzingPaper
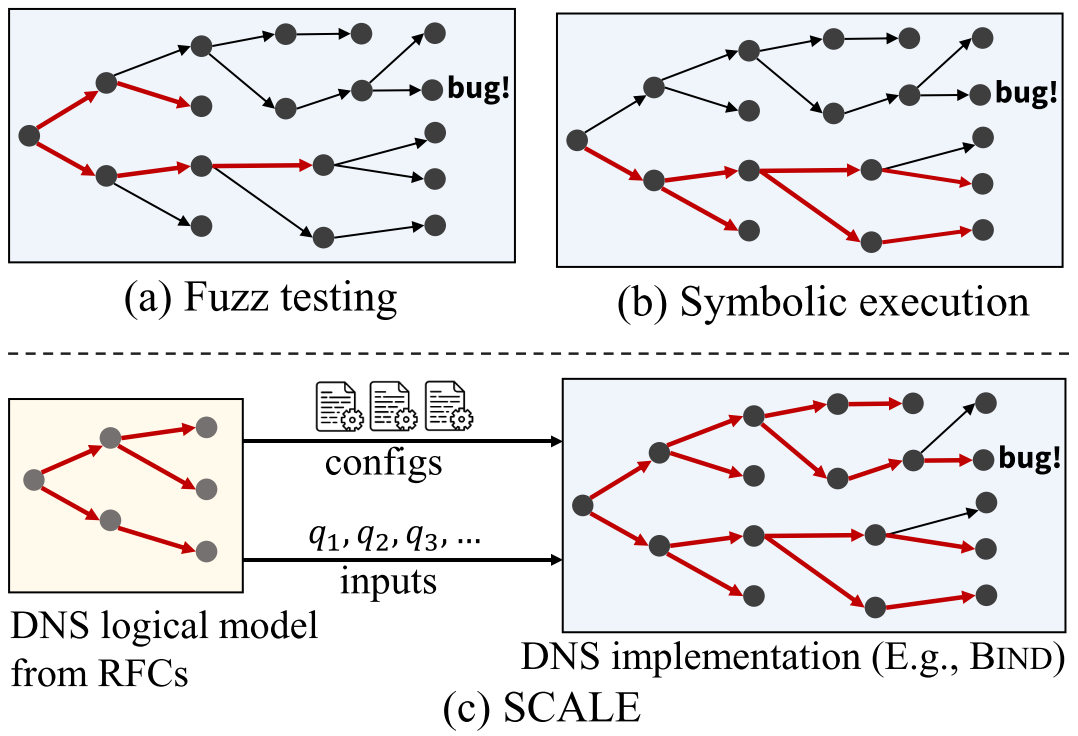
Ferret: Automatically Finding RFC Compliance Bugs in DNS Nameservers
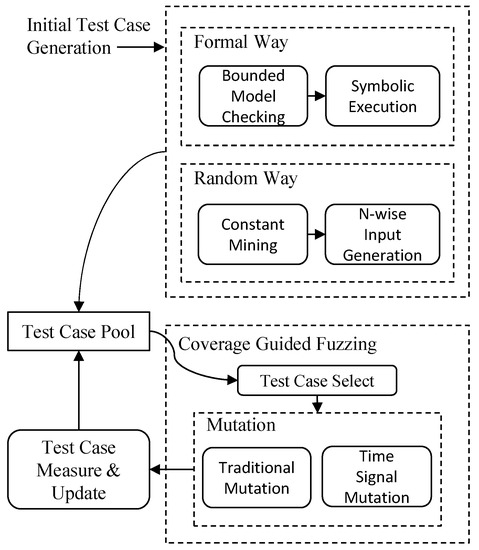
Electronics, Free Full-Text

DeepFuzzer: Accelerated Deep Greybox Fuzzing
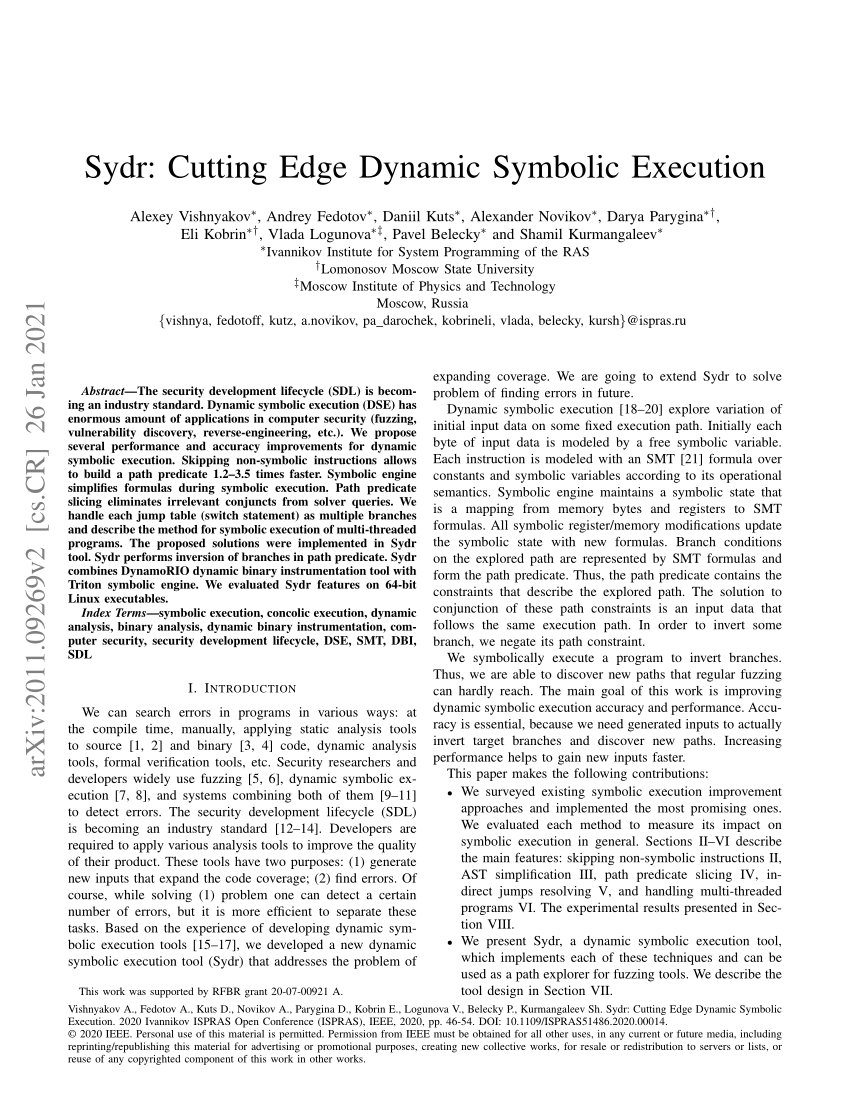
PDF) Sydr: Cutting Edge Dynamic Symbolic Execution
Symbolic Fuzzing - The Fuzzing Book

How to fuzz java code with jazzer? - DEV Community

SAGE: Whitebox Fuzzing for Security Testing - ACM Queue
de
por adulto (o preço varia de acordo com o tamanho do grupo)