Malware analysis Malicious activity
Por um escritor misterioso
Descrição

Endpoint Detection and Response, Free - What is EDR Security?
Lab 6-1 Solutions - Practical Malware Analysis [Book]

Feature Extraction and Detection of Malwares Using Machine Learning

Playbook for Malware outbreak

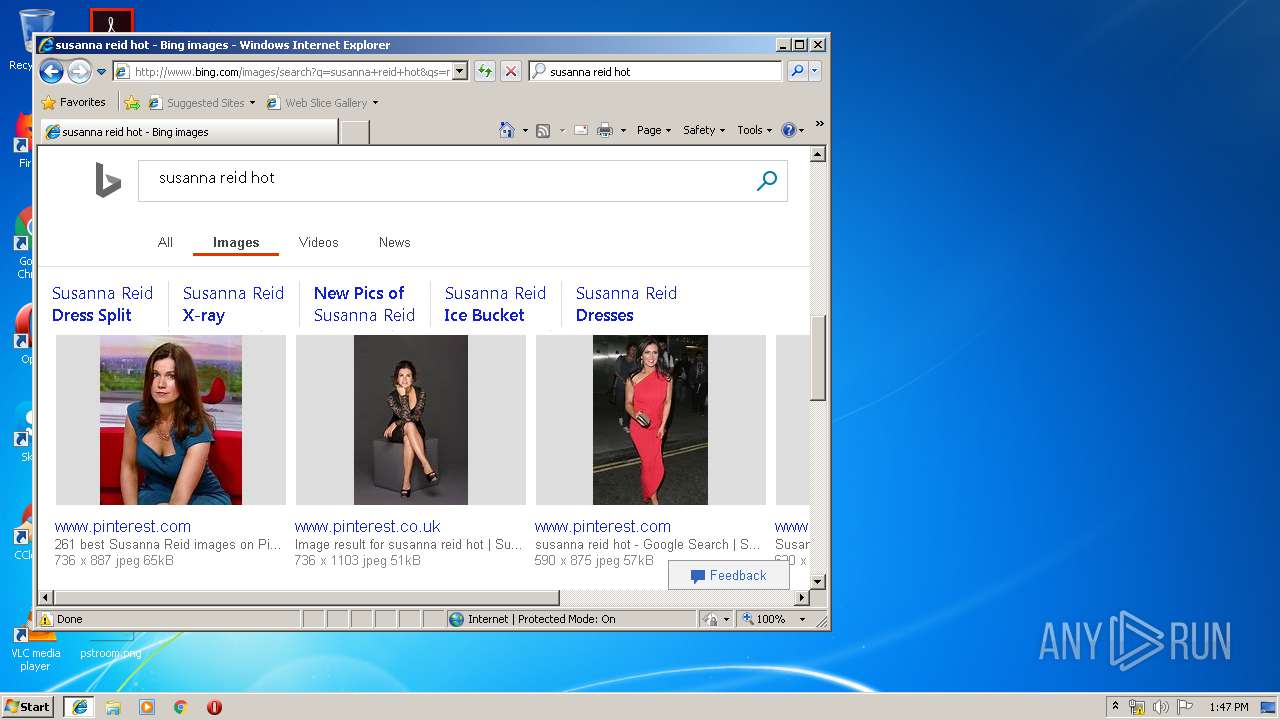
Malware analysis metasploit.bat Malicious activity
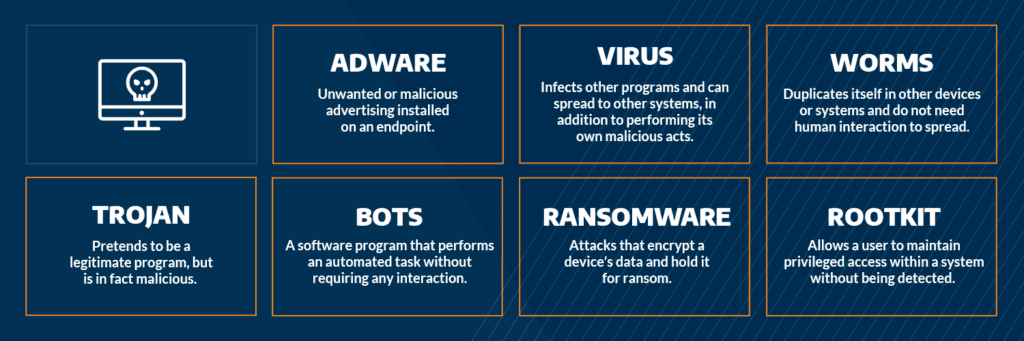
Most Common Malware Attacks
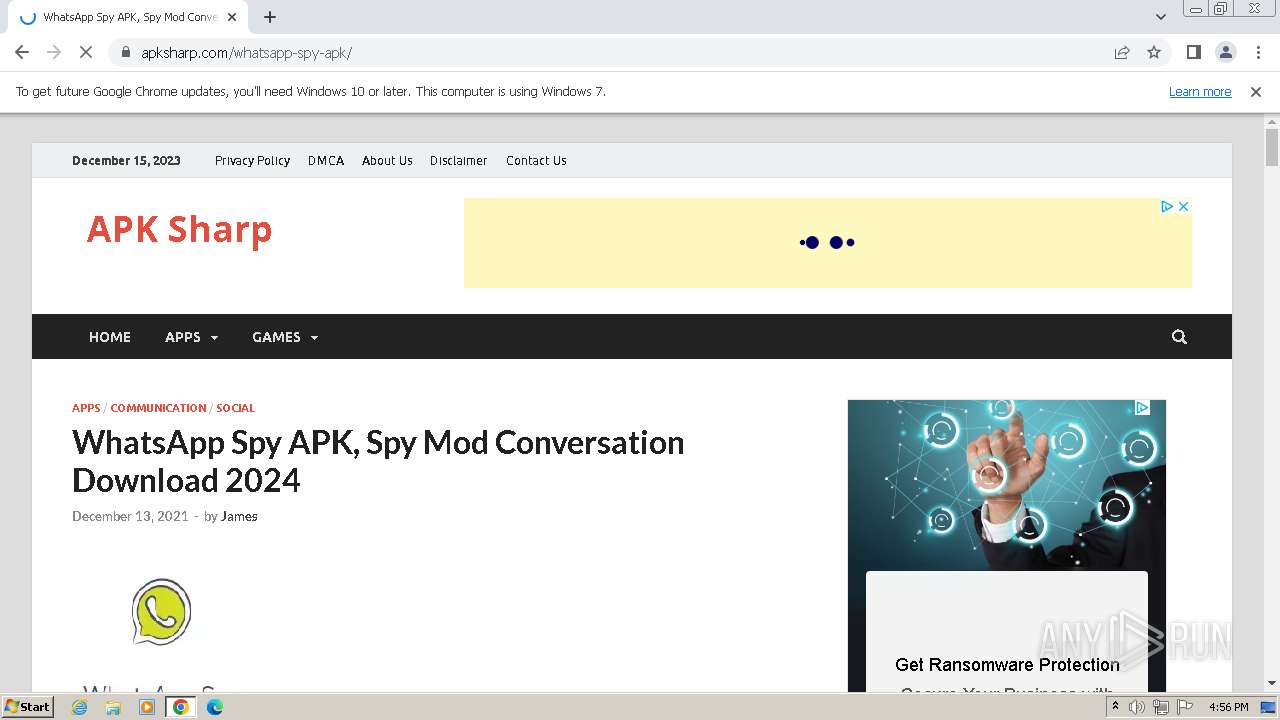
Malware analysis apksharp.com Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike
Malware analysis index.html Malicious activity
Most Common Malware Attacks
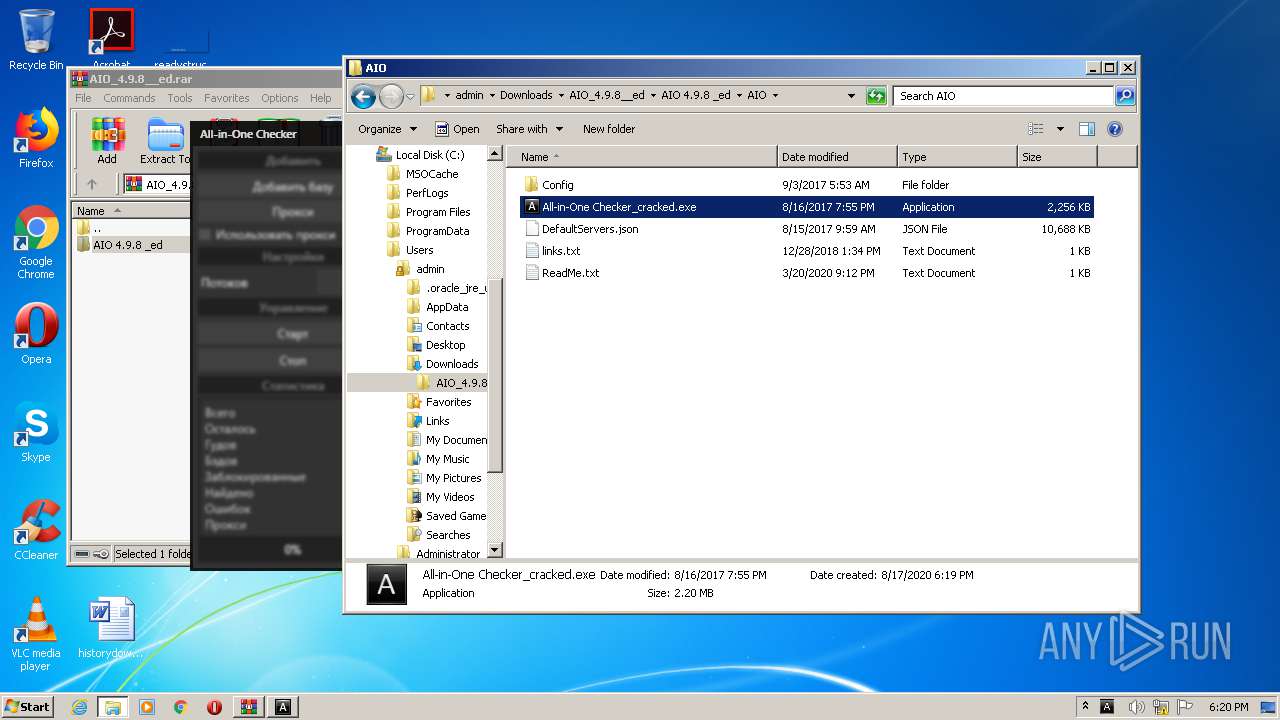
Malware analysis AIO_4.9.8__ed.rar Malicious activity
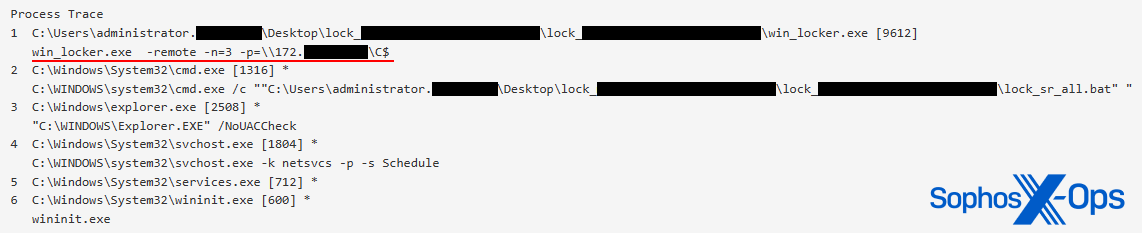
CryptoGuard: An asymmetric approach to the ransomware battle – Sophos News

A detailed analysis of the Menorah malware used by APT34
de
por adulto (o preço varia de acordo com o tamanho do grupo)